MetaOne®'s Approach to Security
Overview
Saakuru All-in-one Crypto App enables users to manage assets 100% on-chain while maintaining 100% control, all without the fear of being the single point of failure.
Saakuru All-in-one Crypto App® uses a Verifiable Secret Sharing (VSS) security protocol, which is a variation of Shamir’s Secret Sharing. Think assisted key management. With our implementation of VSS, seed phrases and private keys are destroyed up front to limit access when it’s not needed. The private key is only regenerated for a few milliseconds, in memory, on an as needed basis (e.g. request signing) after which it is immediately destroyed.
The private key is regenerated using a golden key, which requires multiple pieces of credentials to unlock; one of the required credentials is the user, which also has multi-factor authorization for an extra layer of protection. During the moments when the private key is available, it is protected by memory guard, hardenOS, customized HIPS, and Sandbox to ensure that it cannot be tampered with or stolen.
Users no longer have to manage their own seed phrases and private keys with Saakuru All-in-one Crypto App. Additionally, users are able to recover their access, so there is no chance for them to ever lose access to their assets. Lastly, Saakuru All-in-one Crypto App separates authentication credentials from authorization credentials. This means that even if a hacker can access and see your assets, the hacker still will not be able to touch your assets, especially when we mandate your memory as part of the authorization process.
On top of all that, we guarantee that users will have access to their assets even if AAG no longer exists.
This is self-custody done right.
Why No Seed Phrases?
Seed phrases create a false sense of security, because they are only secure if you know how to manage and use them. For users who want ownership of their assets, it is the most dangerous part of the security scheme, irrespective of the wallet type: software or hardware (aka cold wallet).
A majority of self-custody wallets are created for developers and early adopters who have an understanding about security or who are comfortable trying out new technology. Seed phrases are difficult to commit to memory, thereby resulting in users often finding unsecure solutions to save the phrase. For software and hardware wallets alike, the seed phrase is the key to a user's assets - anyone who has it can approve transactions and use it as the recovery mechanism. For hardware wallets, anyone with the seed phrase can recover and access a user's assets on another similar device.
As we have seen recently, even a core developer for Bitcoin managed to lose 200+ BTC. If cannot be expected of mainstream consumers to have the in depth technical knowledge to manage their own security with seed phrases, and it is extremely irresponsible to ask them to do so.
Beyond Blockchain Security
Our goal is to build a wallet not only for today's users, but to support the (near) future demographic of Web3 users, which we envision to be everyone. Users participating in Web3 may be as young as six years old. Coupling the fact that users will have varying degrees of finance and technology knowledge, and the unforgiving nature of Web3 today, it can pretty much be concluded that none of the existing wallets are safe for mainstream users. This includes MPC wallets, multisig wallets, hardware wallets, etc.
Let’s take a look at two specific examples:
- Users can easily connect their wallets to the wrong dApp because they are easy to clone
- Users can easily make a mistake sending to Solana case-sensitive wallet addresses (which is not the case for other blockchains which do not have case-sensitive wallet addresses). Even if you first send a test transaction, if a user copy and paste again and accidentally change from let’s say capital “E” to lowercase “e” for the last character of the wallet address, the fund will be sent elsewhere.
The goal for Saakuru All-in-one Crypto App is to provide a user friendly experience where users can focus on Web3 activities instead of constant surveillance of their wallet.
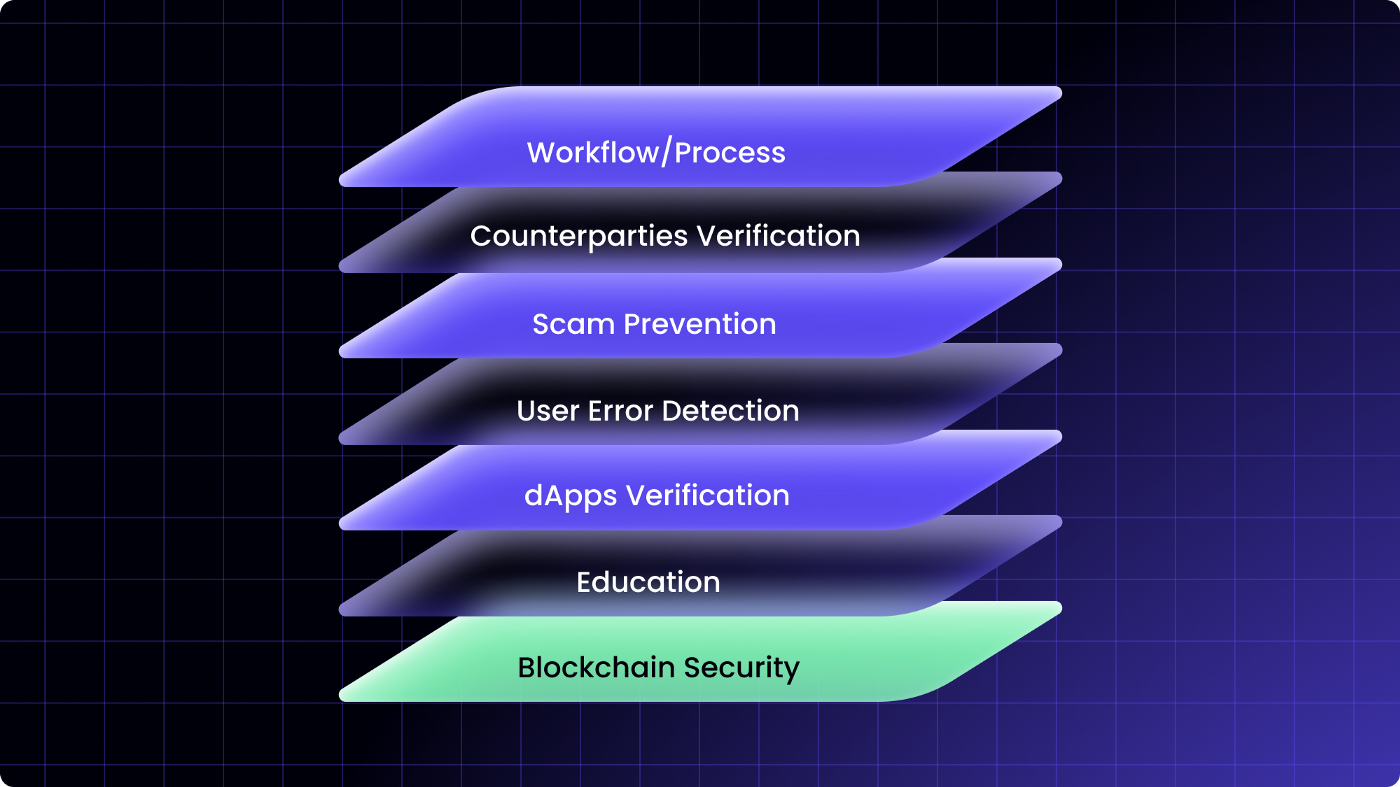
Saakuru All-in-one Crypto App's seven layers of security
Our holistic approach is to provide seven layers of securities, starting with blockchain security as the foundational layer. The various layers will prevent common user mistakes, minimize the chance of getting scammed, and in the worst case, provide a limit as part of the workflow to minimize potential losses. None of these activities can be prevented by blockchain security alone.
We will provide more details on the security use cases in the near future as we continue to educate consumers.
